Embedded (SBCs) are transforming security systems, offering compact yet powerful solutions for real-time data processing and analysis. In this article, we delve into the pivotal role of SBCs in modern security infrastructure. From their architecture to applications, advantages, and future prospects, we explore how SBCs are reshaping the landscape of security technology. Join us as we uncover the advantages, challenges, and innovations surrounding Embedded SBCs, paving the way for more efficient and intelligent security solutions.
Supercharging Security: Embedded SBCs Unveiled
1. Architecture and Components:
Embedded Single-Board Computers (SBCs) are characterized by their compact design, housing all essential components on a single circuit board. Understanding the architecture and components of SBCs provides insight into their functionality and suitability for various applications.
a. Microprocessor:
The microprocessor is the central processing unit (CPU) of an SBC, responsible for executing instructions and processing data. SBCs typically utilize low-power microprocessors, tailored to meet the specific requirements of embedded applications. These microprocessors come in various architectures, including ARM, x86, and RISC, each offering different performance levels and power consumption characteristics.
b. Memory:
Memory modules on an SBC include random-access memory (RAM) for temporary data storage and read-only memory (ROM) for firmware and boot code. The amount of memory available on an SBC varies depending on the specific model and application requirements. SBCs may also support external storage options such as SD cards or solid-state drives (SSDs) for additional data storage.
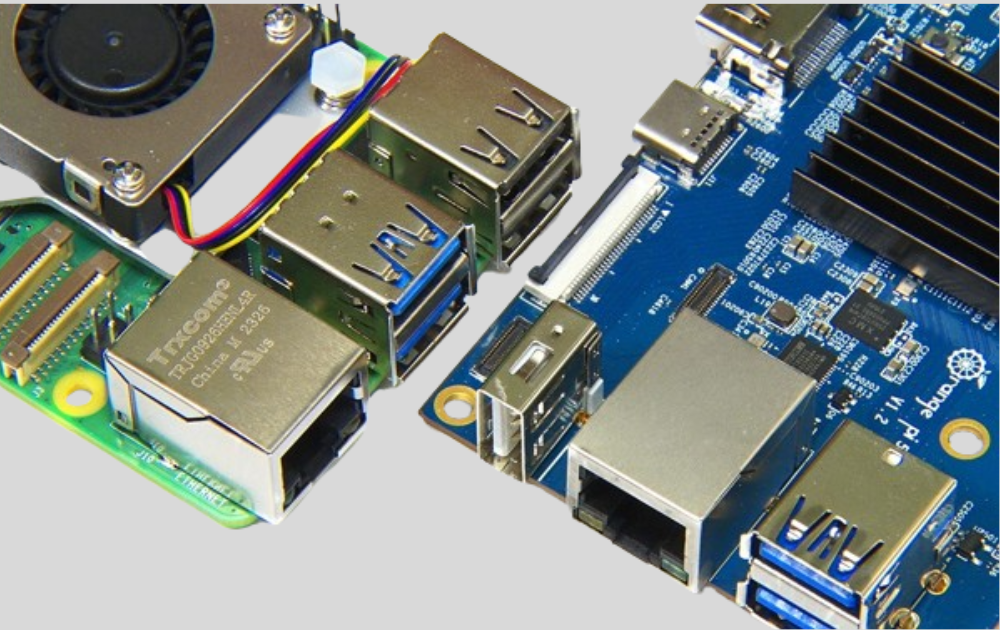
c. Input/Output (I/O) Features:
Embedded SBCs incorporate a range of I/O features to interface with external devices and peripherals. Common I/O interfaces include USB ports, Ethernet ports, serial ports (RS-232/RS-485), GPIO (General-Purpose Input/Output) pins, HDMI or DisplayPort for video output, and audio jacks. These interfaces enable connectivity with sensors, actuators, displays, and other hardware components essential for embedded applications.
d. Power Supply:
Embedded SBCs are designed to operate on low power, making them suitable for battery-powered or energy-efficient applications. They typically accept a wide range of input voltages, allowing flexibility in power supply options. Some SBCs may also support Power over Ethernet (PoE) for simplified power delivery in networked applications.
e. Form Factors:
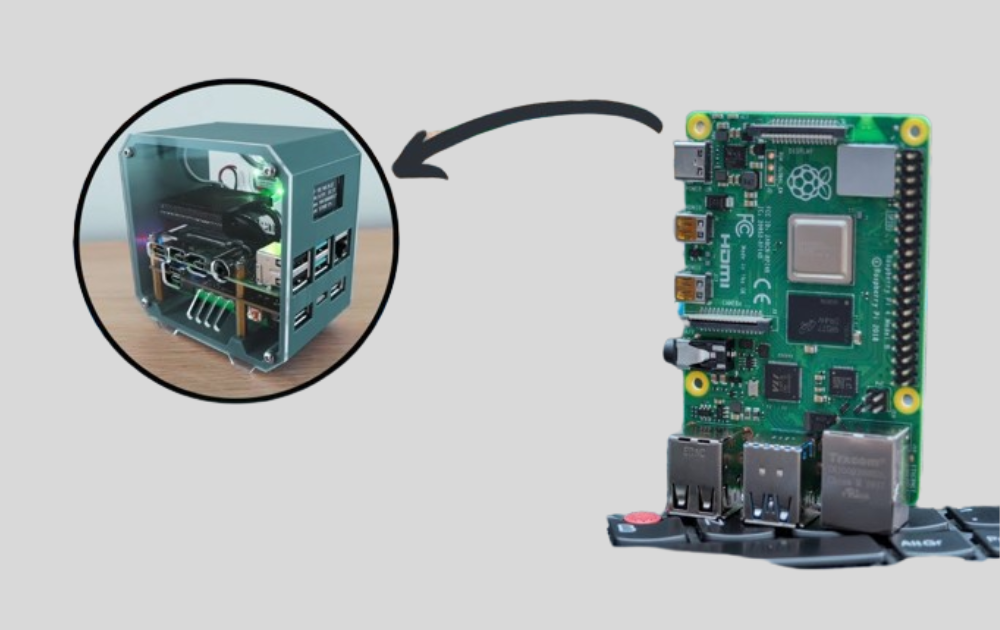
Embedded SBCs are available in various form factors to accommodate different application requirements. Common form factors include the Raspberry Pi form factor, Mini-ITX, COM Express, and PCIe/104™. Each form factor offers unique advantages in terms of size, expansion capabilities, and compatibility with industry standards.
Understanding the architecture and components of embedded SBCs lays the foundation for exploring their advantages and applications in security systems. These compact yet powerful devices form the building blocks of modern security infrastructure, offering unparalleled performance and flexibility in a variety of deployment scenarios.
2. Advantages of Embedded SBCs:
Embedded Single-Board Computers (SBCs) offer a multitude of advantages that make them indispensable in security systems. Understanding these advantages is essential for appreciating the significant role that SBCs play in enhancing security infrastructure.
a. Compactness:
One of the primary advantages of embedded SBCs is their compact size. By integrating all essential components onto a single circuit board, SBCs minimize space requirements and facilitate easy integration into security devices. This compactness allows for the creation of smaller and more discreet security solutions, suitable for a variety of environments and applications.
b. Low Power Consumption:
Embedded SBCs are designed to operate on low power, making them ideal for energy-efficient security systems. Their efficient use of power ensures prolonged battery life in portable devices and reduces overall energy consumption in fixed installations. This low power consumption also contributes to the sustainability and environmental friendliness of security solutions powered by SBCs.
c. High Reliability:
With fewer moving parts compared to traditional computers, embedded SBCs exhibit high reliability and durability. The absence of components such as fans and hard disk drives reduces the risk of mechanical failures, increasing the uptime and longevity of security systems. This enhanced reliability is particularly crucial in mission-critical security applications where system downtime is not an option.
d. Customizability:
Embedded SBCs offer a high degree of customizability, allowing security professionals to tailor systems to meet specific requirements. From selecting the appropriate microprocessor and memory configuration to integrating specialized I/O features and peripherals, SBCs can be customized to address the unique needs of different security applications. This flexibility enables the creation of highly optimized and efficient security solutions that deliver superior performance and functionality.
e. Versatility:
The versatility of embedded SBCs makes them suitable for a wide range of security applications. Whether deployed in access control systems, video surveillance cameras, intrusion detection systems, or biometric identification devices, SBCs excel in diverse security scenarios. Their ability to adapt to various environments and requirements makes them invaluable assets in the design and implementation of comprehensive security solutions.
By harnessing the advantages of embedded SBCs, security professionals can create robust, efficient, and reliable security systems that effectively address the evolving challenges of today’s security landscape. From enhanced performance and flexibility to reduced power consumption and increased reliability, SBCs empower organizations to achieve their security objectives with confidence and efficiency.

3. Applications in Security Systems:
Embedded Single-Board Computers (SBCs) play a crucial role in various aspects of security systems, offering advanced capabilities and versatility that enhance overall performance and functionality. Understanding the diverse applications of SBCs in security is essential for leveraging their potential to address specific security challenges effectively.
a. Real-time Data Processing:
An outstanding feature of embedded SBCs is their ability to process and analyze data in real-time. This real-time processing is particularly critical in security applications where timely response is paramount. SBCs enable the execution of complex algorithms for tasks such as facial recognition, object detection, and motion tracking, allowing security systems to detect and respond to threats swiftly and accurately.
b. Integration into Security Devices:
Embedded SBCs can be seamlessly integrated into various security devices to enhance their functionality and performance. Whether deployed in access control systems, surveillance cameras, or intrusion detection sensors, SBCs serve as the computational backbone, enabling advanced features such as biometric authentication, video analytics, and intelligent decision-making. Their compact size and versatility make them ideal for integration into a wide range of security devices, regardless of form factor or application requirements.
c. Enhanced Security Operations:
By leveraging the computational power of embedded SBCs, security operations can be significantly enhanced. SBCs enable the processing and analysis of large volumes of data, allowing security personnel to identify patterns, anomalies, and potential threats more effectively. This enhanced situational awareness enables proactive security measures, such as predictive analytics and threat modeling, leading to improved overall security posture and risk mitigation.
d. Versatile Deployment Scenarios:
Embedded SBCs are deployed in diverse security scenarios, ranging from commercial facilities and residential properties to critical infrastructure and public spaces. Their versatility allows them to adapt to various environments and requirements, providing reliable and efficient security solutions across different sectors and industries. Whether deployed in indoor or outdoor settings, SBC-based security systems excel in delivering robust protection and real-time monitoring capabilities.
e. Scalability and Future-Proofing:
The scalability of embedded SBCs enables security systems to evolve and expand as needs change over time. Whether scaling up to accommodate larger facilities or integrating new technologies and features, SBC-based security systems offer flexibility and adaptability to meet evolving security requirements. Additionally, the future-proofing capabilities of SBCs ensure that security investments remain relevant and effective in the face of emerging threats and technological advancements.
By harnessing the diverse applications of embedded SBCs in security systems, organizations can create comprehensive and effective security solutions that address a wide range of threats and challenges. From real-time data processing and enhanced security operations to versatile deployment scenarios and scalability, SBCs empower organizations to achieve their security objectives with confidence and efficiency.